Nexus Market Link: System Analysis
An objective review of the technical infrastructure, historical development, and cryptographic standards employed by the Nexus Market hidden service.
Executive Summary
Nexus Market Link is a decentralized e-commerce platform operating within the Tor network as a hidden service. Launched to fill the vacuum left by the closure of previous market entities, Nexus was designed with a specific focus on "Walletless" architecture, attempting to mitigate the risk of centralized cryptocurrency seizure (exit scams).
Unlike traditional escrow markets that require users to deposit funds into a site-controlled wallet, Nexus Market Link utilizes a direct payment system. This system generates a unique payment address for every order, aiming to ensure that funds move directly from the buyer to the settlement phase without lingering in a central hot wallet.
Technical Architecture
CRYPTOCURRENCY SUPPORT
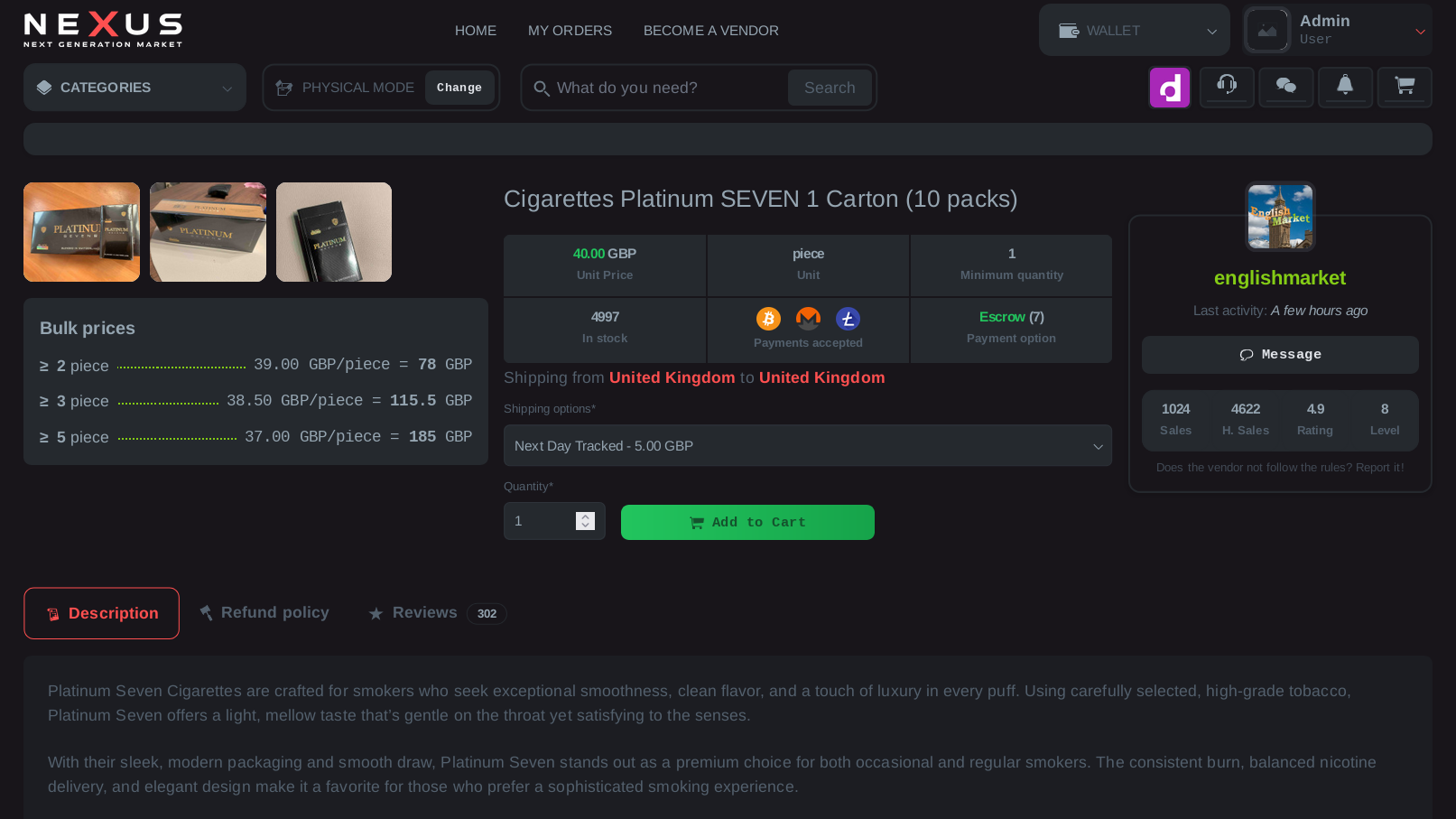
The platform supports a multi-chain environment to facilitate transactions.
- Bitcoin (BTC) SegWit Compatible
- Monero (XMR) Subaddress Enforced
- Litecoin (LTC) MWEB Supported
SECURITY PROTOCOLS
Mandatory encryption standards required for all participants.
- PGP 2FA Mandatory on Login
- Mirror Verification RSA-4096 Signatures
- Data Retention Auto-Wipe 14 Days
Operational Timeline
Platform Inception
PHASE I - DEPLOYMENTNexus Market Link establishes its initial .onion root structure. Early beta testing focuses on load balancing across the Tor network to prevent DDoS attacks common to the ecosystem.
Monero Integration
PHASE II - PRIVACY ENHANCEMENTResponding to blockchain analysis heuristics, the platform enforced XMR (Monero) as a primary settlement layer, encouraging privacy-centric transactions over transparent ledgers like Bitcoin.
Walletless Pay Upgrade
PHASE III - RISK MITIGATIONThe current iteration of the market deprecated the central wallet model in favor of per-order invoice generation, significantly reducing the "honey pot" risk for all users.
System Interface